Freedom to
Like magic
Abion empowers brands and fuels innovation.
- innovate
- dream
- grow
We safeguard your brand
You keep going
Combining heart and tech, our brand protection experts are just a phone call away, always going that extra mile. Abion creates a safe existence for your brand, we call it Brand Freedom.
Customer cases
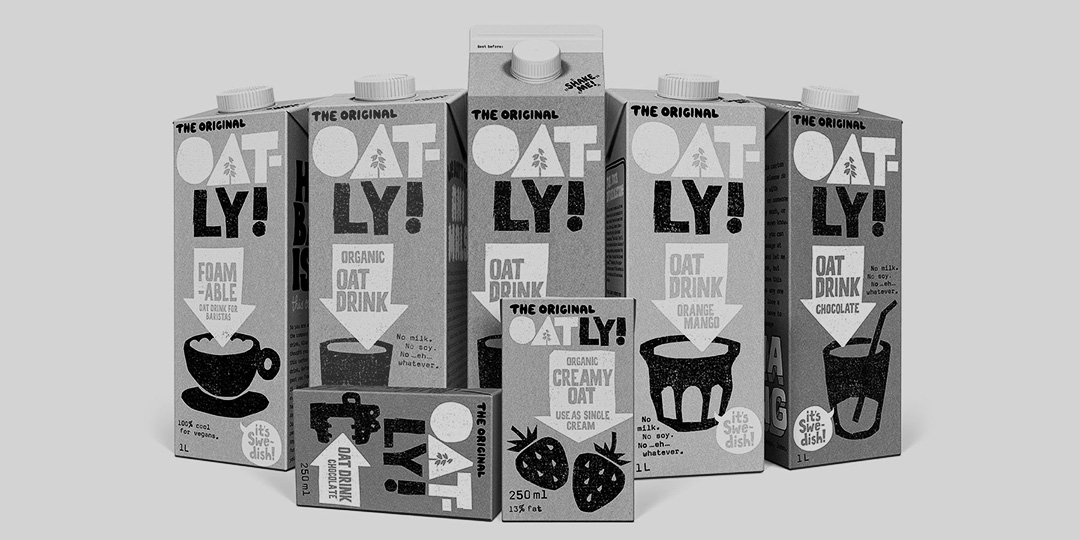
Problems solved – brands empowered
What we do
Expertise in all aspects of brand protection

Enjoy effortless brand protection
Our cutting-edge platform lets you manage and gain comprehensive insights into everything concerning your brand, domains, trademarks and web security services. Discover a smarter way to manage your brand.
Insight & News
Knowledge Hub

Harry Bose Workshop Sign-Up

5 famous cases of counterfeiting